-
【中国新闻网】“GEEKCON2025”上海站收官 业界共探AI与机器人安全等新挑战
-
【上海电视台】聚焦人工智能等前沿领域 GEEKCON 2025上海站今日开幕
-
【上海电视台】聚焦人工智能等前沿领域 GEEKCON 2025上海站开幕
-
【第一财经】一道语音指令让从未接入互联网的机器人破防,于是它开始了攻击……
-
【新华网】“GEEKCON2025”上海站收官 业界共探AI与机器人安全等新挑战
-
【南方都市报】大赛现场,人形机器人被黑客劫持
-
【IT时报】直击机器人“叛变”现场:机器人打人!还感染同伴
-
【信息时报】“GEEKCON2025”上海站收官 人工智能与机器人安全成焦点
-
【南方都市报】谁来保护隐私?极棒现场70秒攻破漏洞,AI眼镜是偷拍利器
-
【中国日报】“GEEKCON2025”上海站在沪收官 人工智能与机器人安全成焦点
-
【新闻晨报】“GEEKCON2025”上海站在沪收官 人工智能与机器人安全成焦点
-
【数说安全】GeekCon上的那一拳,打碎了具身智能的安全幻觉
-
【安在】GEEKCON 2025上海站闭幕:现已种下“不让世界变坏”的安全火种
-
【嘶吼】记GEEKCON2025上海:在没有天花板的地方,让安全向下扎根,向上生长
-
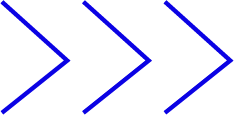
【清华大学】我院学生参与的Redbud&AOSP联合战队获GEEKCON 2025“漏洞与利用DAF挑战赛”赛道冠军
-
【IT之家】“GEEKCON2025”上海站在沪收官 人工智能与机器人安全成焦点
-
【FREEBUF】“GEEKCON2025”上海站在沪收官 人工智能与机器人安全成焦点
-
【安全客】GEEKCON 2025上海站收官:人工智能与机器人安全引关注
HONOR ROLL
Updates ongoing.


Redbud & AOSP Union Team

One Computer — Within Seconds, Half of Global Services Become Unreachable?

Yunfan Zhan

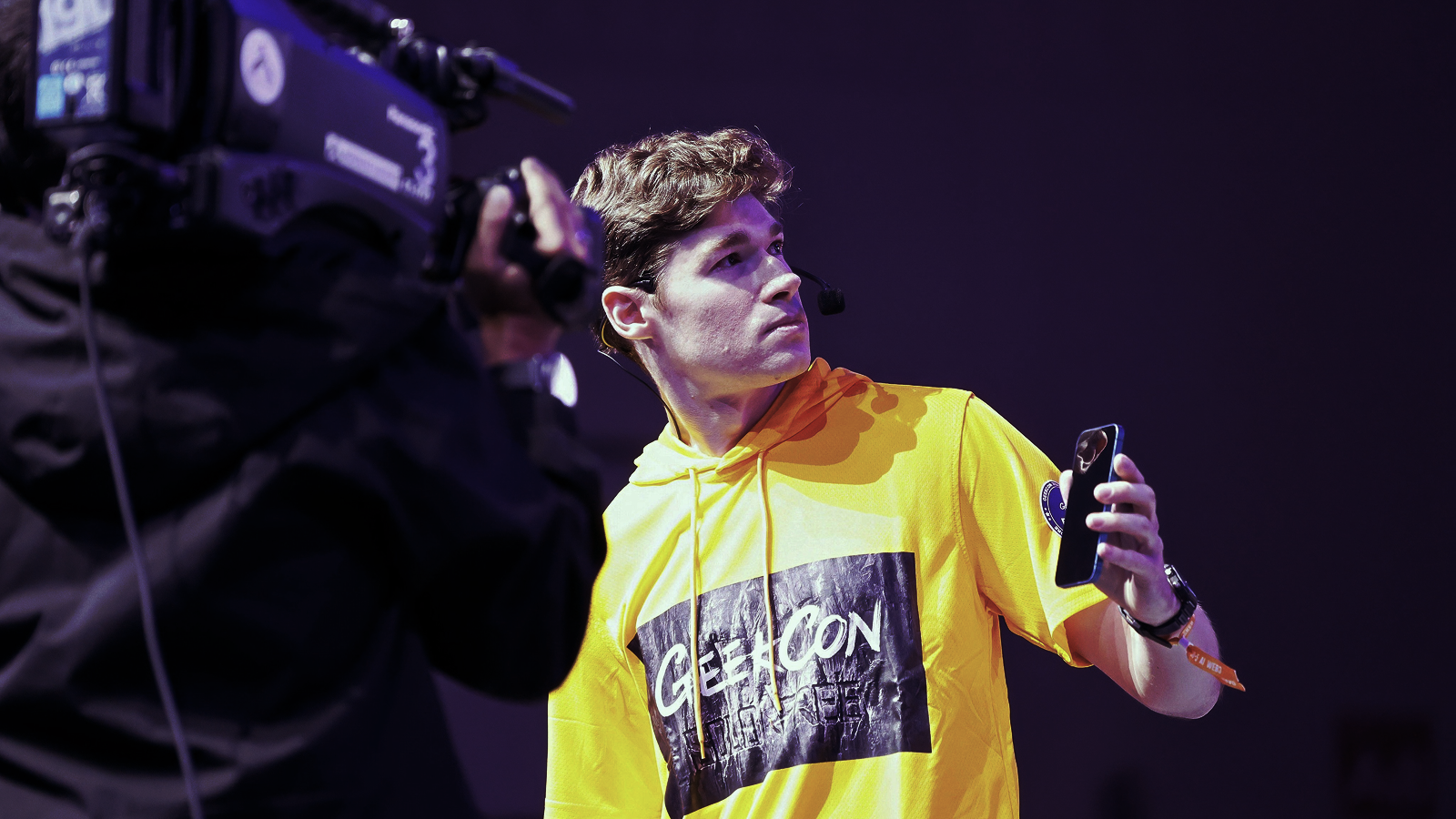
Protector vs. Predator: Have Crypto Wallets Become Gateways for Looting?
Yunfan Zhan

Xianrui Dong

Your Glasses, My Eyes
Xianrui Dong

Wuying Security Lab

Smart — But Not Much
Wuying Security Lab


Google Android Red Team (US)

Fighting cavities: Securing Android Bluetooth by Red teaming
Google Android Red Team (US)

Postive Technologies (RU)

Buried in the Log. Exploiting a 20 years old NTFS Vulnerability
Postive Technologies (RU)

Fengyu Liu (LFY) - Fudan University

Make Agent Defeat Agent: Automatic Detection of Taint-Style Vulnerabilities in LLM-based Agents
Fengyu Liu (LFY) - Fudan University

Nan Wang (sakura), Ziling Chen (R1nd0)

Null to RCE: Breaking V8 through WebAssembly GC Type Exploits
Nan Wang (sakura)
Ziling Chen (R1nd0)

Yufan Liu (X1r0z)

Hacking GraalVM Espresso Abusing Continuation API to Make ROP-like Attack
Yufan Liu (X1r0z)

Xuangan Xiao, Zikai Xu

The Biometric AuthToken Heist: Cracking PINs and Bypassing CE via a Long-Ignored Attack Surface
Xuangan Xiao
Zikai Xu

Shipei Qu, Zikai Xu

Mechanical Awakening or Out of Control? Just One Line of Code
Shipei Qu
Zikai Xu

Gewu Lab

Is Your Drone Still Listening to You?
Gewu Lab

Discloser: Confidential

No Installation, No Escape from Scams
Discloser: Confidential

Hidden Corners
NEW FOCUS
Value through Confrontation
COMMITTEE
Either the No. 1, or the Only 1.
RESTRICTIONS & NOTIFICATIONS
Professionalism is to try our best.
1 GEEKCON organizing committee (hereinafter referred to as "the committee") recognizes the technical capability of the winner individually, but doesn't acknowledge that it represents the capability of the winner's working organization.
2 The committee recognize and promote the comprehensive assessment of vulnerability exploitation capabilities and mitigation mechanisms from a confrontational perspective, and do not endorse the judgement of security levels of the target products involved in the event based on a single dimension or non-quantitative dimension.
3 The committee firmly follows the Responsible Disclosure principle. The committee and contestant commit not to disclose any details to third-party before manufactures fix the issues.
4 The committee advocates and encourages in-depth knowledge sharing and communication, but firmly opposes any speech and behavior that violates laws and regulations or infringes on the rights of others.
5 The committee guarantees that the participants' personal information will not be disclosed to third-party or used for commercial activities without their agreement and authentication.
6 The committee will provide awards and honors based on the research efforts, technical breakthrough, and technical innovation of the projects. As the top 1 security geek IP operator in China, the committee always advocate a reward mechanism that emphasizes both honor and moderate bounty, encouraging more geeks to participate in technical innovation and knowledge sharing.
THANKS TO THE SECURITY COMMUNITY
Geeks, solo but not alone.






































Contact
Registration Desk:
Business&Media Cooperations: